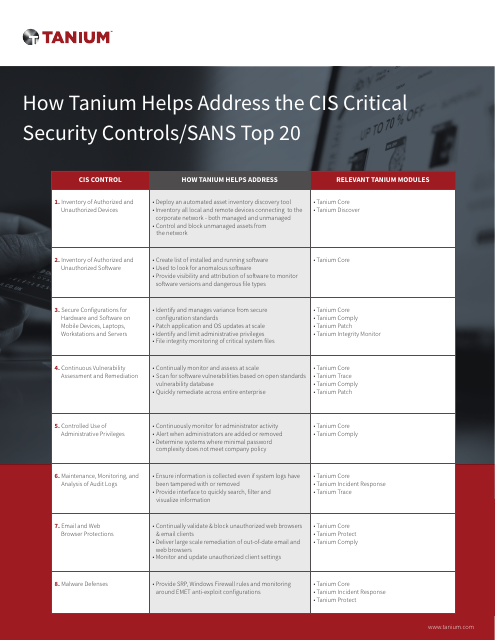
How Tanium helps address the CIS Critical Security Controls/SANS Top 20 | Cyentia Cybersecurity Research Library

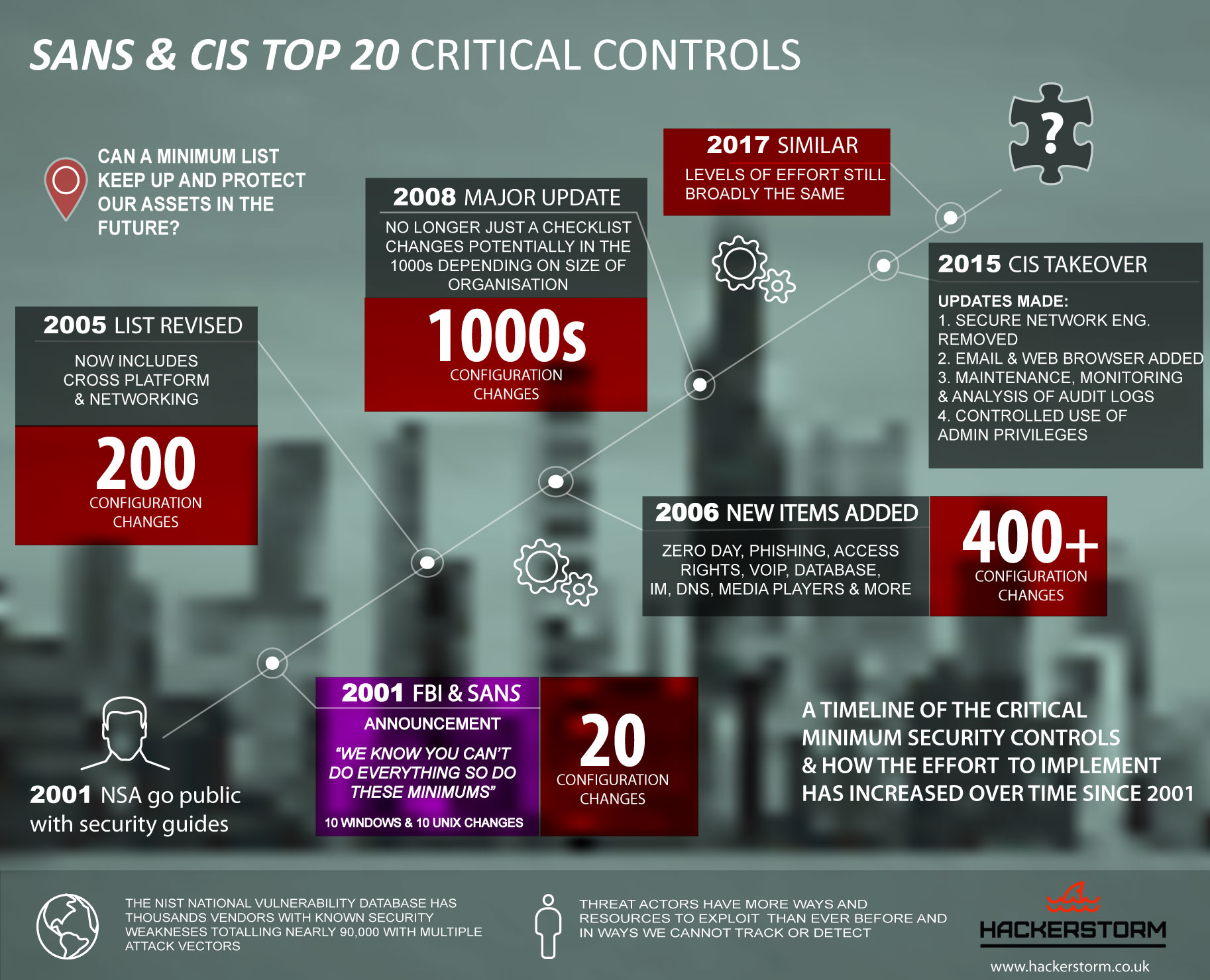
At least 3 of SANS top 20 Critical Controls require addressing SSH key based access & SSH key management to know who can access what & enforce boundary.
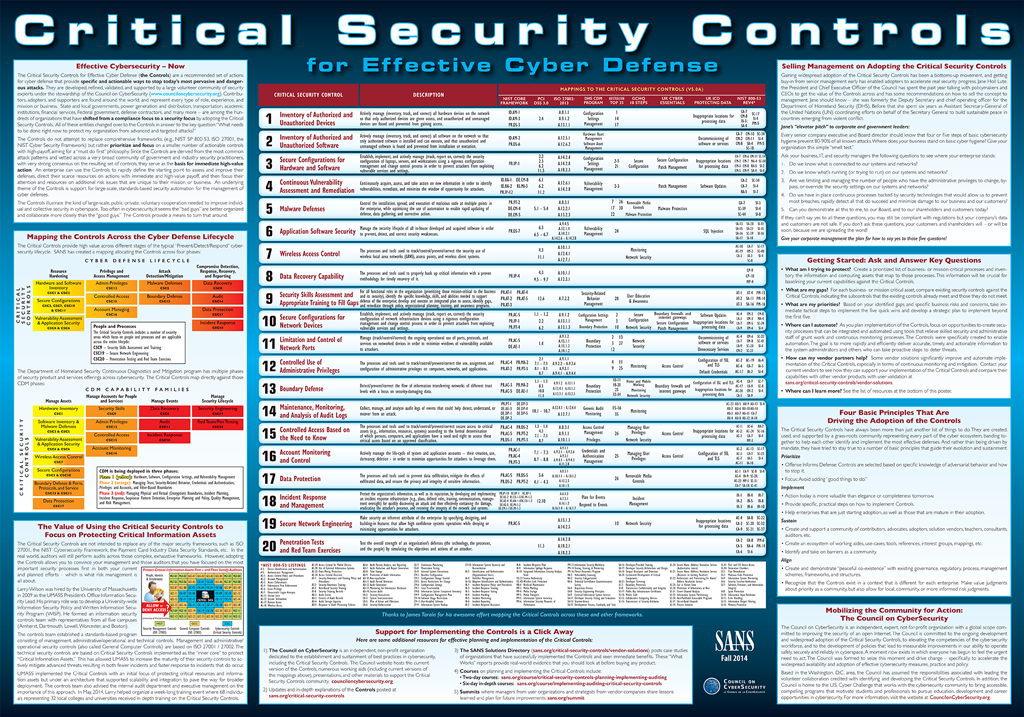
SANS Institute on X: "20 CRITICAL SECURITY CONTROLS | POSTER: Set of actions for cyber defense. DL > PDF (2pgs) - http://t.co/YZGlCbuXmd http://t.co/moeIozrqu0" / X